What are IoT security solutions?
IoT security solutions refer to the set of technologies, policies, and practices designed to protect connected devices and the networks they operate within. These devices, ranging from smart sensors and surveillance cameras to medical equipment and industrial systems, form what we call the Internet of Things (IoT).
Unlike traditional IT assets, IoT devices are often built with a focus on functionality rather than security. This means they may lack built-in protections such as strong authentication, encryption, or the ability to receive frequent updates. As a result, IoT cybersecurity is not just about protecting endpoints; it’s about securing an entire ecosystem of interconnected devices.
At a high level, effective connected device security focuses on three pillars: controlling access to the network, ensuring secure communication, and maintaining visibility over all connected assets. These pillars form the foundation of any modern IoT security strategy.
Why IoT environments are uniquely vulnerable
IoT environments introduce a level of complexity that traditional IT security models were not designed to handle. Enterprises today may have thousands of connected devices spread across offices, stores, hospitals, or facilities, often managed by different teams or vendors.
This creates an expanding attack surface. Each connected device becomes a potential entry point for attackers, especially when devices are deployed with default credentials, outdated firmware, or minimal security controls. In many cases, organizations don’t even have a complete inventory of what’s connected to their network.
As IoT adoption increases, so does the need for security solutions that are specifically designed to handle this scale and diversity.
Why is IoT device security challenging?
Securing IoT devices is fundamentally different from securing laptops, servers, or mobile devices. The challenge is not just technical, it’s architectural.
One of the main issues is that many IoT devices have limited computing power. They are not designed to run traditional security tools such as antivirus software or endpoint detection agents. This means security teams cannot rely on the same controls they use in standard IT environments.
Another major challenge is the lack of standardization. IoT devices come from a wide range of manufacturers, each using different operating systems, communication protocols, and security models. This fragmentation makes it difficult to apply consistent security policies across all devices.
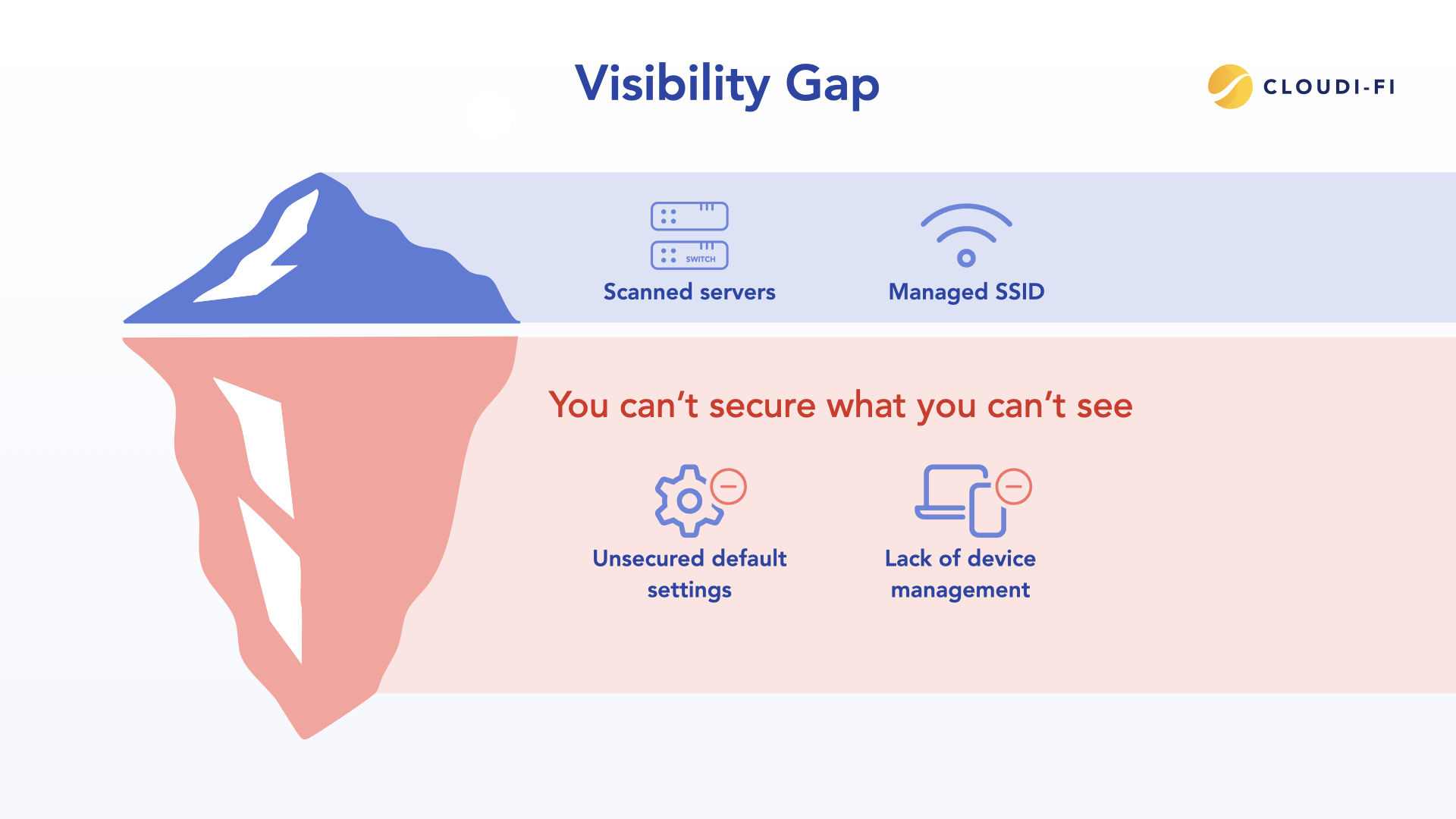
Visibility is also a persistent problem. In many organizations, IoT devices are connected by different departments without going through IT, leading to a growing number of unmanaged IoT devices. For example, facilities teams might install smart HVAC systems, while retail teams deploy connected POS devices. Without centralized oversight, these devices can remain “invisible” to security teams.
Finally, IoT devices often have long lifecycles. A device installed today might still be in use 5–10 years from now, long after its security mechanisms are outdated. This creates ongoing exposure to known vulnerabilities.
Together, these factors make IoT device security particularly challenging and highlight the need for specialized IoT security solutions.
IoT security risks and solutions: Understanding the threat landscape
To effectively secure IoT environments, organizations must first understand the risks they face. The IoT threat landscape is evolving, but many vulnerabilities remain consistent across industries.
Common IoT vulnerabilities
IoT devices are frequently deployed with inherent weaknesses that can be exploited if not addressed. These include weak or hardcoded passwords, unpatched firmware, insecure communication protocols, and a lack of proper authentication mechanisms.
For a deeper dive into these issues, you can explore our blog post on IoT device vulnerabilities. These vulnerabilities are not just theoretical, they are actively exploited in real-world attacks.
Types of attacks
- Attackers target IoT environments using a variety of techniques, often combining multiple methods to achieve their goals.
- Botnet attacks are one of the most well-known examples. In these scenarios, attackers compromise large numbers of IoT devices and use them to launch distributed denial-of-service (DDoS) attacks.
- Unauthorized access is another common threat. Devices with weak authentication can be easily taken over, giving attackers direct control.
- Perhaps the most dangerous risk is lateral movement. Once an attacker gains access to a single IoT device, they can use it as a foothold to move deeper into the network, potentially reaching critical systems.
Mapping risks to solutions
Addressing these risks requires a layered approach. Strong authentication mechanisms can prevent unauthorized access, while network segmentation limits the ability of attackers to move laterally. Continuous monitoring helps detect unusual behavior early, allowing teams to respond before damage is done.
This alignment between risks and controls is essential for effective IoT risk management.
Why IoT security is critical for businesses
The importance of IoT security has grown significantly in recent years as the number of connected devices continues to increase.
Increase in IoT attacks
Cybercriminals are increasingly targeting IoT devices because they are often easier to exploit than traditional IT systems. High-profile incidents have demonstrated how insecure devices can be leveraged at scale.
A well-known example is the Mirai botnet, which infected thousands of IoT devices and used them to disrupt major online services.
This attack highlighted how seemingly harmless devices can be weaponized when not properly secured.
Business risks
For organizations, the consequences of poor IoT security can be severe. A single compromised device can lead to data breaches, operational disruptions, or compliance violations.
For example, in a healthcare environment, an unsecured medical device could expose sensitive patient data. In retail, compromised POS systems could lead to financial fraud. In smart buildings, attackers could disrupt critical infrastructure such as heating or access control systems.
Beyond immediate operational impact, these incidents can also result in long-term reputational damage and loss of customer trust.
Key features of effective IoT security solutions
Effective IoT security solutions are built around several core capabilities that work together to protect devices and networks.
1. Device authentication and identity management
At the foundation of IoT security is the ability to identify and authenticate every device that connects to the network. Without this, organizations cannot distinguish between trusted and untrusted devices.
Modern solutions use techniques such as certificate-based authentication and integration with Identity and Access Management (IAM) systems. This ensures that only authorized devices are allowed to connect, reducing the risk of unauthorized access.
2. Network segmentation and access control
Not all devices should have the same level of access. Network segmentation allows organizations to isolate IoT devices into separate zones, preventing them from interacting directly with critical systems.
Access control policies can then be applied based on device type, role, or behavior. For example, a surveillance camera should not have access to financial systems.
This approach significantly reduces the potential impact of a security breach.
3. Threat detection and response
Given the dynamic nature of IoT environments, real-time threat detection is essential. Security solutions must be able to identify unusual patterns of behavior, such as a device communicating with unexpected destinations.
Increasingly, organizations are using AI-based tools to analyze device behavior and detect anomalies. When a threat is identified, automated responses, such as isolating the device, can help contain the risk.
4. Data encryption and secure communication
IoT devices often transmit sensitive data, making secure communication critical. Encryption protocols such as TLS help ensure that data cannot be intercepted or tampered with during transmission.
In addition, secure APIs and communication channels help protect interactions between devices and backend systems.
5. Continuous monitoring and asset visibility
Visibility is one of the most important aspects of IoT security. Organizations need a clear understanding of what devices are connected, where they are located, and how they behave.
Continuous monitoring allows security teams to track device activity in real time, identify anomalies, and maintain an up-to-date inventory of assets.
Without this level of visibility, it is nearly impossible to enforce effective security policies.
Types of IoT security solutions for enterprises
Enterprises typically rely on a combination of different security solutions to protect their IoT environments.
- Network-based security solutions focus on controlling access and monitoring traffic at the network level. These include technologies such as Network Access Control (NAC), firewalls, and intrusion detection systems.
- Endpoint or device-level security solutions focus on securing individual devices through firmware updates and embedded protections. While important, these are often limited by the capabilities of the devices themselves.
- Cloud-based IoT security solutions provide centralized visibility and management. They allow organizations to monitor devices across multiple locations and enforce policies remotely, making them ideal for large-scale deployments.
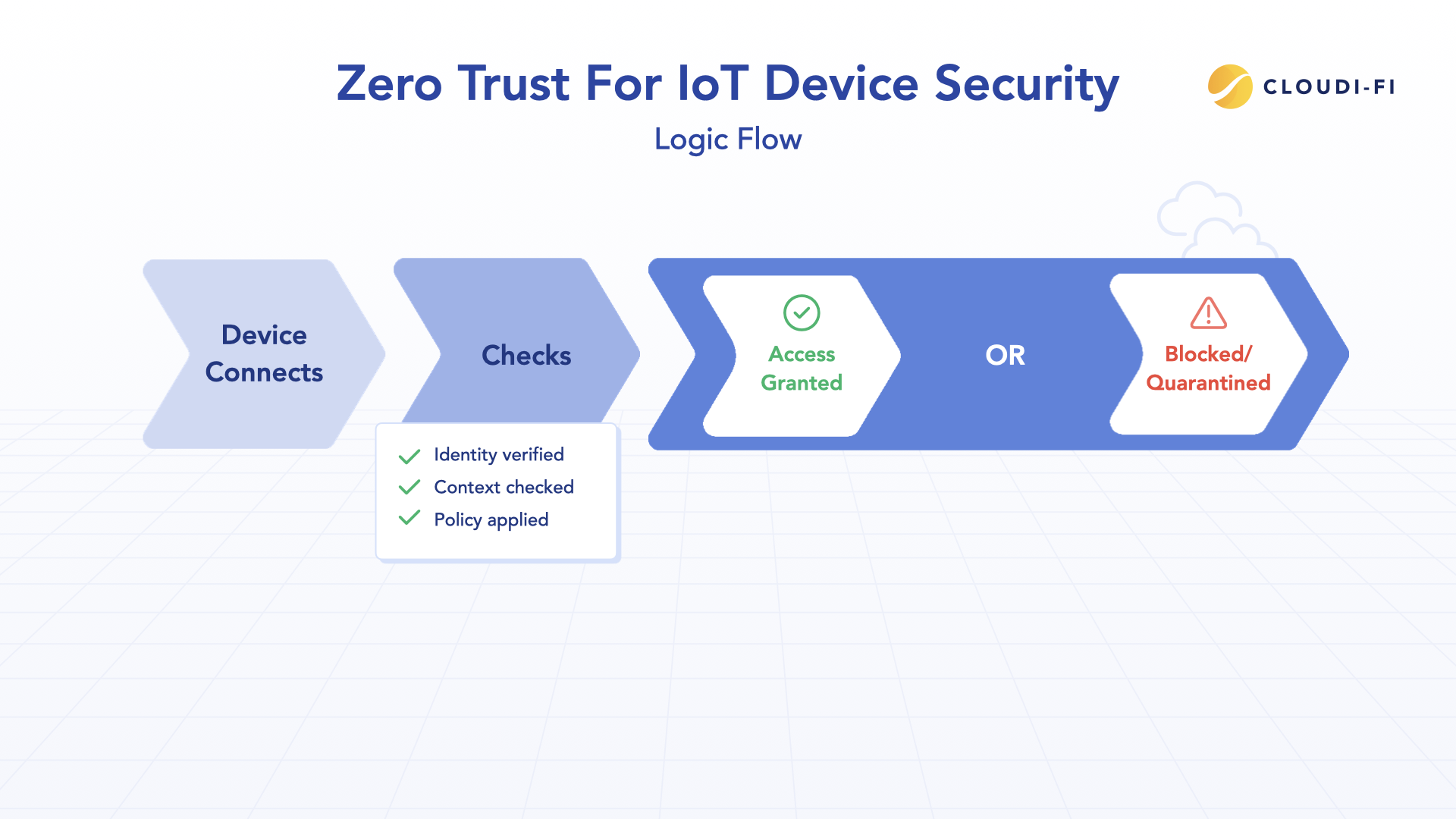
- Finally, Zero Trust IoT security solutions take a more holistic approach. Based on the principle of “never trust, always verify,” they require continuous authentication and enforce strict access controls across the network.
Best IoT security solutions for enterprises
Rather than focusing on specific vendors, it’s more useful to think in terms of solution categories.
- Network Access Control (NAC) solutions are a foundational component. They provide visibility into connected devices and enforce access policies based on identity and context.
- IoT-specific firewalls are designed to handle device-level traffic, helping prevent unauthorized communication between devices or with external systems.
Together, these solutions form the backbone of modern IoT network security solutions.
Why Network Access Control is critical for IoT security
Among all available approaches, Network Access Control stands out as particularly effective for IoT environments. One of its biggest advantages is that it does not require agents to be installed on devices. This makes it suitable for a wide range of IoT devices that cannot support traditional security software.
NAC solutions also provide compatibility across device types. They can identify and classify devices based on their behavior, even when those devices are unknown or unmanaged IoT devices. Perhaps most importantly, NAC enables organizations to implement a Zero Trust model. By authenticating every device and enforcing access policies continuously, it ensures that only authorized devices can interact with the network, and only in approved ways.
This makes NAC a critical component of any IoT network access control strategy.
How to secure IoT devices in a network
Securing IoT devices starts with visibility. Organizations must first identify all connected devices and understand their role within the network. From there, they can enforce authentication, segment devices into appropriate network zones, and monitor activity continuously.
Regular updates and policy enforcement ensure that security is maintained over time, even as new devices are added.
How to choose the right IoT security solution
Selecting the right IoT security solution requires careful consideration of your organization’s needs and environment.
- Scalability is essential, especially for enterprises with large or distributed deployments. The solution should be able to handle thousands of devices without compromising performance.
- Integration is equally important. A good solution should work seamlessly with existing network infrastructure, security tools, and workflows.
- Compliance requirements must also be taken into account, particularly in regulated industries such as healthcare or finance.
- Finally, ease of deployment can make a significant difference. Solutions that can automatically discover devices, integrate quickly, and enforce policies in real time are more likely to succeed in complex environments.
Best practices for securing IoT devices
While technology plays a key role, best practices are equally important in maintaining a secure IoT environment.
Regular firmware updates help address known vulnerabilities, while strong authentication prevents unauthorized access. Network isolation ensures that devices cannot easily interact with critical systems, and continuous monitoring enables rapid detection of threats.
Together, these practices form the foundation of effective IoT vulnerability management.
Common IoT security challenges (and how to overcome them)
One of the biggest challenges in IoT security is device diversity. With so many different types of devices, applying consistent security controls can be difficult. Network-based approaches help address this by enforcing policies regardless of device type.
Another challenge is the lack of standardization across vendors and technologies. Organizations can overcome this by implementing centralized frameworks and policies that apply across the entire network.
Use Cases
In retail environments, IoT devices such as POS systems, cameras, and inventory sensors are essential for daily operations. Securing these devices ensures that payment systems remain protected and operational. In healthcare, connected medical devices and monitoring systems play a critical role in patient care. Strong security measures are necessary to protect sensitive data and ensure system reliability.
Smart buildings rely on connected systems for HVAC, lighting, and access control. Proper segmentation prevents these systems from exposing corporate networks to risk.
In hospitality, guest Wi-Fi networks and smart room devices must be carefully separated from operational systems to prevent unauthorized access.
Future of IoT security: Zero Trust and network-based control
The future of IoT security is being shaped by several key trends. AI-driven security solutions are becoming more advanced, enabling faster and more accurate threat detection. At the same time, Zero Trust architectures are gaining widespread adoption as organizations seek to secure increasingly complex environments.
In this evolving landscape, network-based control will remain a critical enabler, providing the visibility and enforcement capabilities needed to secure IoT environments at scale.
FAQ Section
What are IoT security solutions?
IoT security solutions are tools and strategies used to protect connected devices, networks, and data from cyberthreats.
How do you secure IoT devices?
By identifying devices, enforcing authentication, segmenting networks, monitoring activity, and applying regular updates.
What are the biggest IoT security risks?
Key risks include weak authentication, unpatched vulnerabilities, unauthorized access, and lateral movement within networks.
Are cloud-based IoT security solutions safe?
Yes, when properly configured, they provide scalable visibility, centralized management, and strong security controls.