Cloud Network Access Platform
Unlock Universal Zero Trust with a secure and global solution
Trusted by 200+ enterprises worldwide
































Unlock the full potential of Cloudi-Fi
A feature-rich platform that empowers you to make informed decisions and drive your business forward with confidence
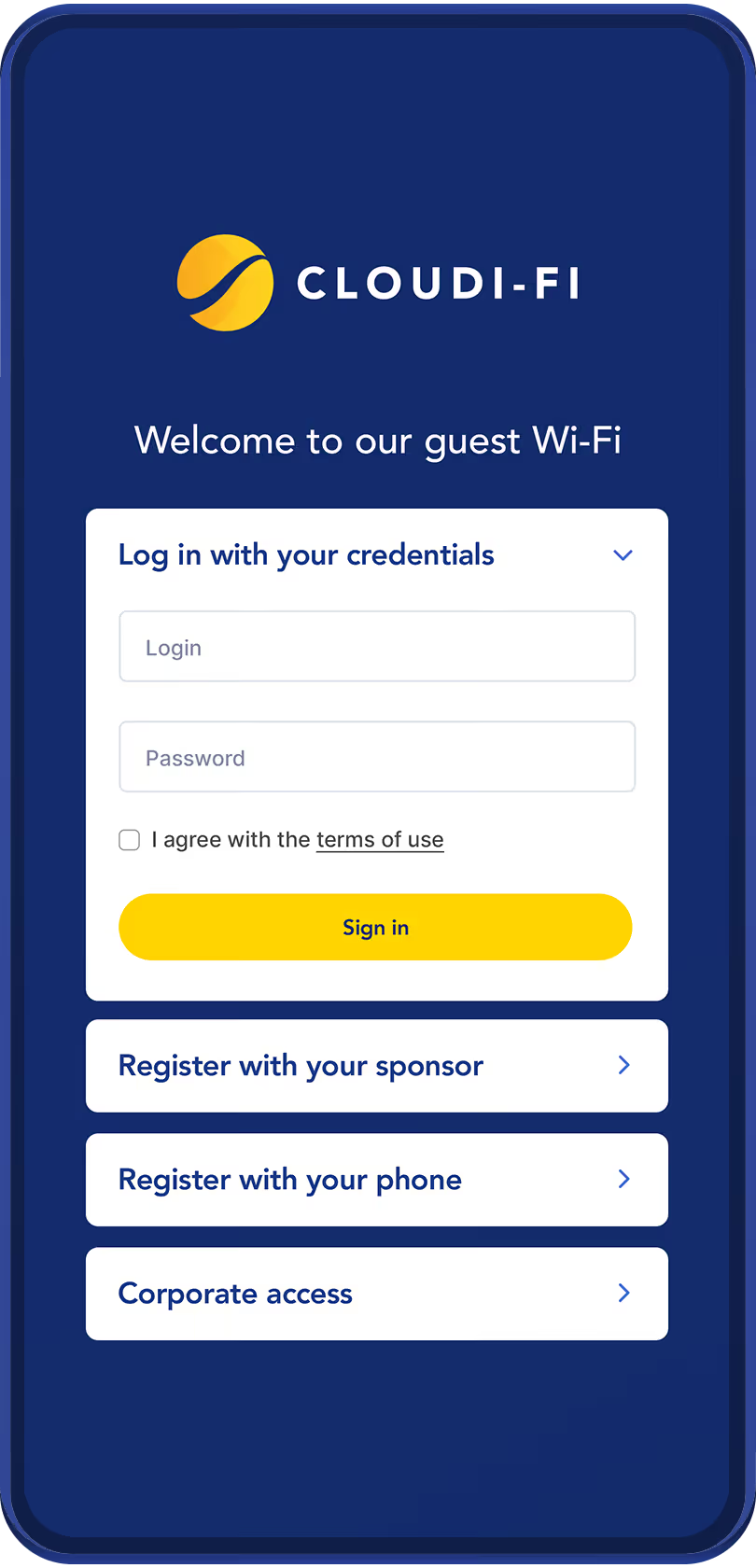
Captive Portal
Cloud-based with centralized user and device authentication.
Offers flexible Wi-Fi onboarding for guests, BYOD users, and employees thanks to social logins, custom forms, SAML, and corporate identity providers.
Compliance
Effortless global compliance with role-based access
Seamless Integration
Easy deployment with any physical and cloud infrastructure
Analytics
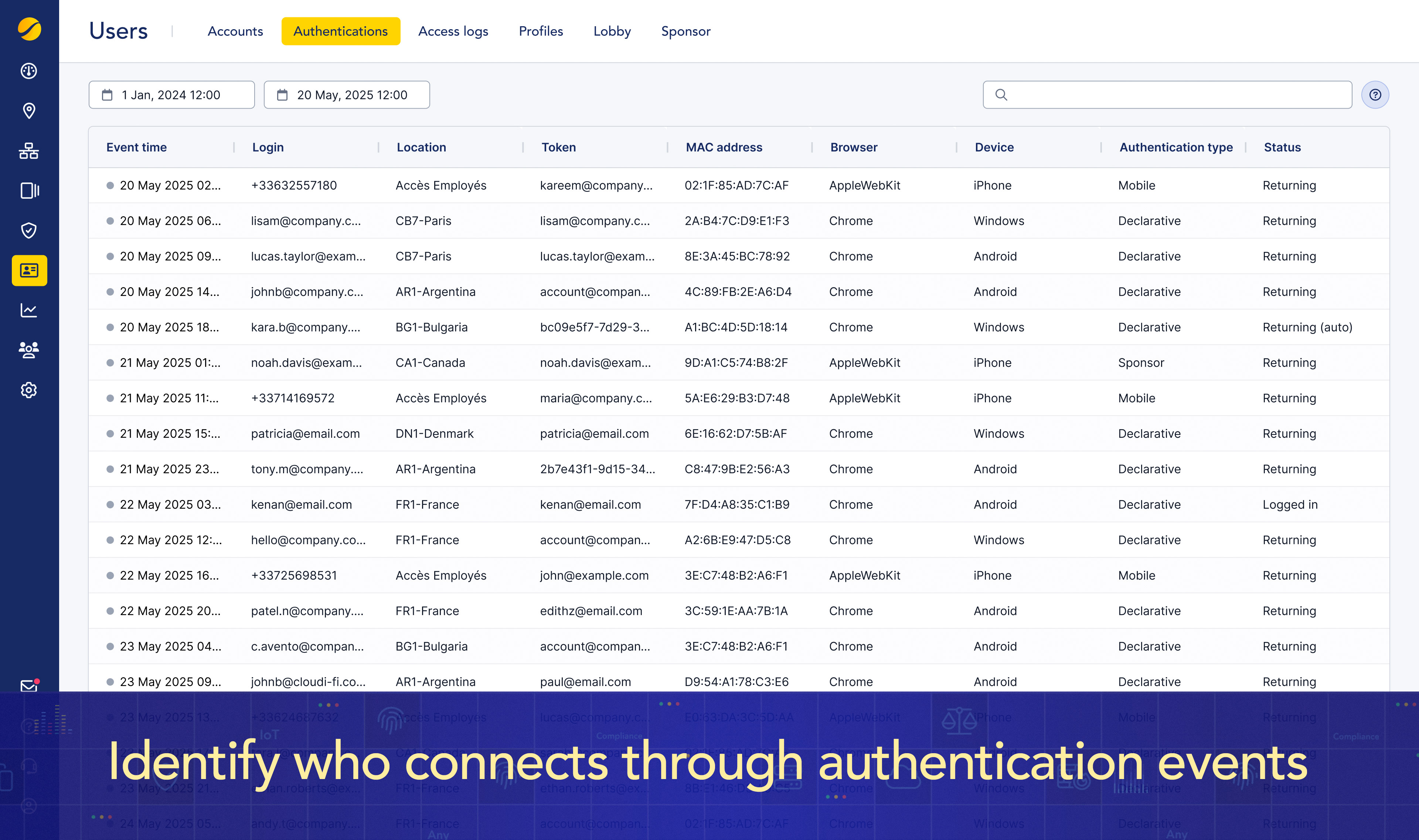
Full network access visibility across all sites and devices
Zero Trust security
Strict identification and authentication for every connection, ensuring robust access control

IoT/OT onboarding
Cloud-DHCP fingerprinting for seamless IoT/OT onboarding, identity control, and shadow IT risk reduction

Integrated with the best technologies on the market
Infrastructure agnostic and plug-and-play deployment: rapidly roll-out Cloudi-Fi across global sites with any infrastructure provider
Cloud native, borderless, scalable and global!
Unlocking Universal Zero Trust Network Access on all continents


Start your journey with Cloudi-Fi

One platform for all businesses
Cloudi-Fi empowers organizations with a scalable, cloud-based solution to secure users, devices, and data.
Designed to integrate seamlessly into existing infrastructures.







.jpg)
