The role of Identity and Access Management (IAM) has fundamentally transformed. What was once considered a supporting IT function has evolved into the primary control plane for enterprise security.
This transformation is not incremental. It is structural.
Widespread cloud adoption, SaaS proliferation, hybrid work, API-driven integrations, and the explosion of machine identities have permanently dismantled the traditional network perimeter. In this borderless environment, identity is no longer a peripheral security layer. It is the only consistent and enforceable boundary.
This is the story of the evolution of IAM: from perimeter-based authentication to identity-driven access in the era of Zero Trust identity.
IAM foundations: The core hasn’t changed, the context has
At its core, IAM answers a simple but persistent question:
Who can access what, under which conditions, and for how long?
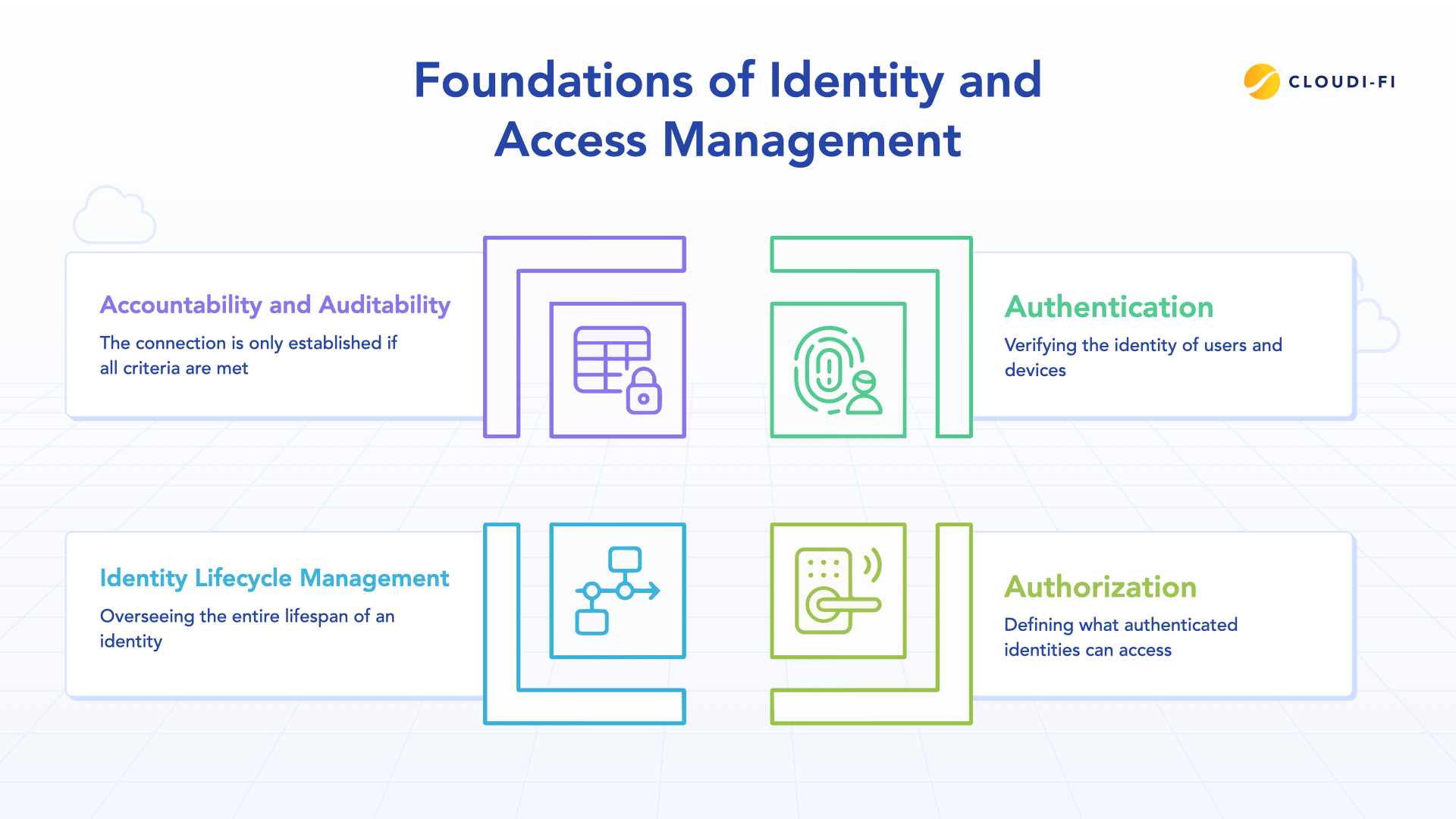
Despite decades of change, IAM still rests on four foundational pillars:
1. Authentication: Establishing identity
Verifying that an identity—whether human or machine—is authentic and who or what it claims to be is the process of authentication.
In the past, this procedure was frequently oversimplified and dependent on risky techniques:
- Static password and username combinations.
- Physical smart cards or simple one-time passcodes (OTPs).
- Kerberos-based ticketing systems heavily reliant on the internal network.
Authentication answers: “Are you who you claim to be?”
Traditional authentication relied on a high degree of implicit trust, primarily based on the user's network location, such as being in the corporate office or connected through a VPN.
2. Authorization: Defining permissions
Determining exactly what an authenticated identity is allowed to view, access, or alter is the process of authorization. In essence, it converts an authenticated identity into a set of restrictions that may be applied to particular resources. The basic query, "What are you allowed to do and see?" is addressed.
Typical and developing authorization models consist of:
- Permissions are categorized according to the user's job function (e.g., "HR Manager" or "Read-Only Auditor") under role-based access control (RBAC). Despite its historical dominance, this paradigm has the potential to become inflexible and unchanging.
- Access decisions under Attribute-Based Access Control (ABAC) are dynamic and determined by a combination of pertinent variables, such as the user's department, location, time of day, and resource sensitivity.
- Policy-Based Access Control (PBAC) is an advanced version of ABAC that uses comprehensive policies to control access in intricate settings.
Authorization was frequently fixed and organized according to hierarchical job roles in older settings. Because employees kept permissions from prior positions that were never terminated, this arrangement frequently resulted in privilege buildup over time.
3. Identity lifecycle management
Identity Lifecycle Management (ILM) governs identities from creation to termination:
- Provisioning (Onboarding): Initiating the identity and granting the essential, baseline access rights when an individual joins the organization or an identity is first established.
- Role modification: Continuously updating permissions to align with evolving responsibilities, such as when an identity changes roles or moves to a new project.
- Deprovisioning (Offboarding): The crucial final stage where all access rights are immediately revoked and the identity is subsequently archived or deleted upon the employee's departure.
When lifecycle management is manual or poorly automated, organizations face:
- Orphaned accounts: Accounts that remain active and accessible long after the employee has left the company.
- Privilege creep: The gradual accumulation of unnecessary or excessive permissions over time.
- Elevated insider risk: Unnecessary continued identity access poses a security risk.
Lifecycle governance is not administrative overhead — it is foundational security infrastructure.
4. Accountability and auditability
Accurate logging, traceability, and availability for review of all access activities are essential. This is critical for both compliance and effective incident response.
This supports:
- Detailed logging
- Regulatory compliance (GDPR, HIPAA, SOX)
- Incident response readiness
Every action must be attributable to a verified identity.
The mission of IAM has remained consistent. What has changed is the environment in which it operates.
IAM before the cloud: The perimeter era
- Centralized infrastructure and implicit trust
Before cloud adoption, enterprise infrastructure was centralized and predictable.
- Applications lived in corporate data centers
- Active Directory served as the identity backbone
- Network segmentation controlled internal access
- Remote access relied on VPN
The core security principle was simple and flawed: Internal = Trusted, External = Untrusted.
- VPN: Extending the perimeter
Remote users gained access almost exclusively via Virtual Private Networks (VPNs).
The critical failing of the VPN model was its architecture:
- It grants network-level access: Once authenticated, the user is logically placed inside the corporate network.
- It enables lateral movement: The user often gains broad visibility to the entire network segment, allowing an attacker who compromises the account to move freely to find high-value targets.
- Access was typically overprovisioned: Users received access to far more than they needed to do their specific task.
VPN extended the network perimeter, it critically did not redefine or limit trust.
- Static and rigid access models
Pre-cloud access decisions were characterized by their rigidity:
- Role-based: Permissions were fixed to a job title.
- Ticket-driven: Relying on Kerberos or similar internal technologies.
- Manually updated: Changes to permissions were often slow, requiring manual intervention.
- Infrequently reviewed: Privilege creep was an inevitable result of this static approach.
- Pre-cloud IAM limitations
Even within the centralized perimeter, challenges were significant:
- Manual provisioning: Slow, error-prone onboarding and offboarding.
- Password dependency: Reliance on easily compromised or phished credentials.
- Limited visibility: Especially into high-risk accounts managed locally on servers.
- Poor Cross-System Integration: Siloed identity stores across different applications.
However, the centralized nature of the infrastructure lent a degree of stability, limiting the complexity of identity integration. That stability ended abruptly with cloud adoption.
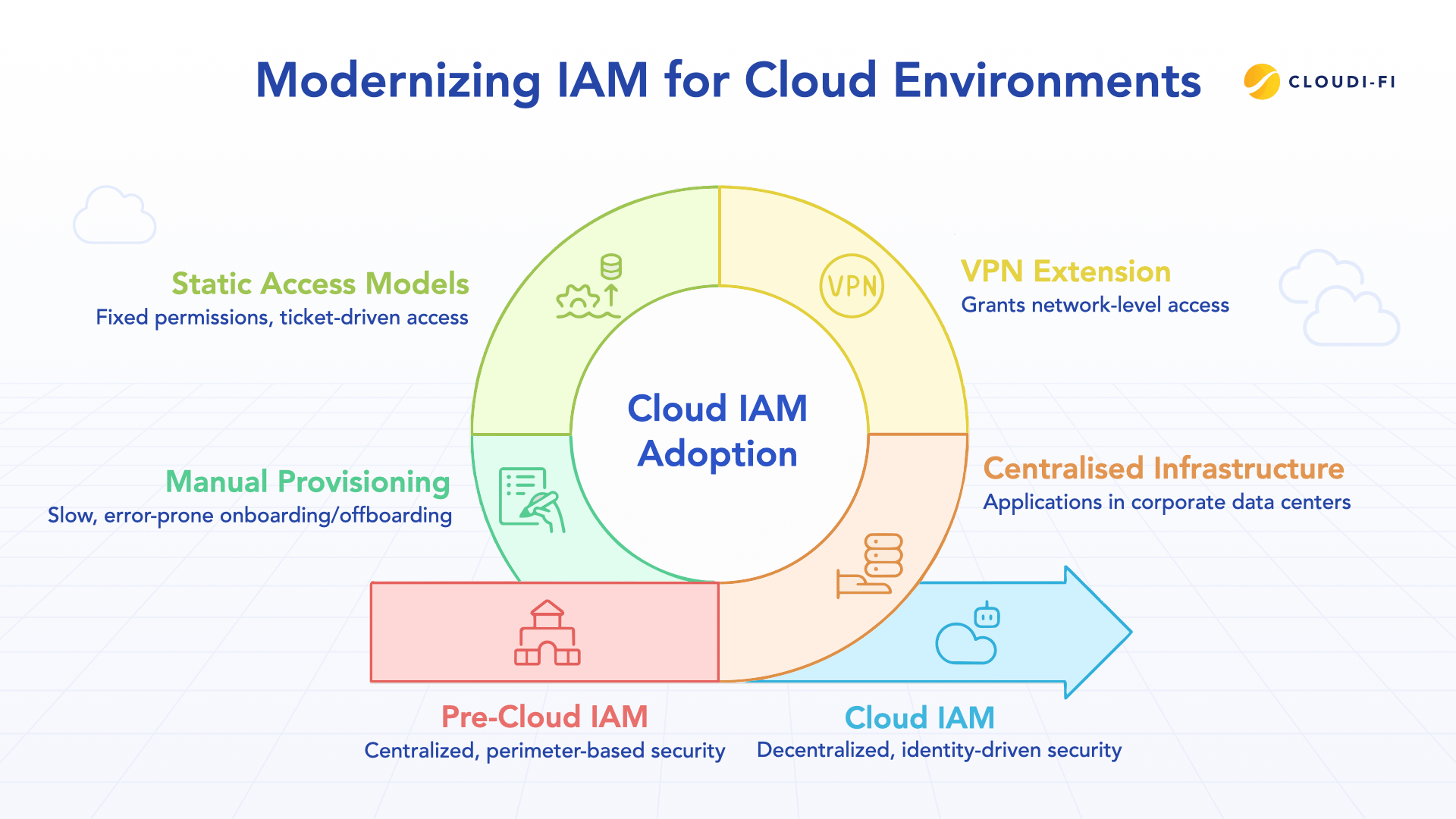
Cloud disruption: The dissolution of the perimeter
Cloud computing was not just a technological migration. It was an architectural disruption.
Enterprise environments became:
- SaaS-driven
- Multi-cloud
- API-connected
- Hybrid and remote
- BYOD-enabled
- Machine-identity heavy
Infrastructure became ephemeral — containers, microservices, and serverless workloads replaced static servers.
The perimeter dissolved into countless access points.
In this distributed environment, the network is no longer a reliable trust boundary.
Identity is.
Modern IAM architecture: Identity as the control plane
The need to secure a complex, distributed cloud environment forced IAM to evolve rapidly, leading to the development and widespread adoption of new core capabilities.
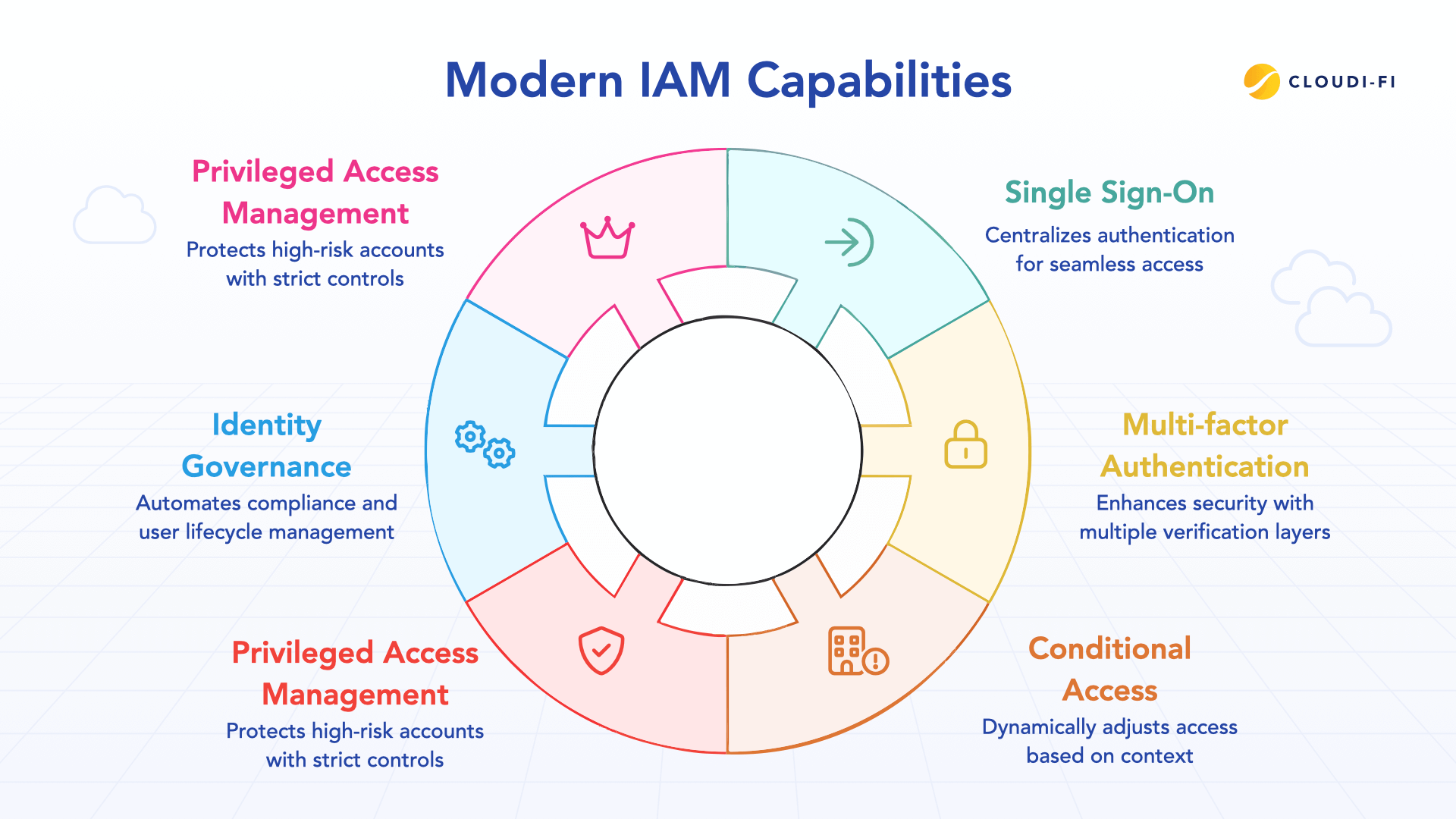
Single Sign-On (SSO)
SSO centralizes authentication across SaaS, cloud, and internal applications using protocols such as SAML and OIDC.
Impact:
- Reduced credential sprawl
- Centralized policy enforcement
- Improved visibility
Multi-Factor Authentication (MFA)
MFA requires multiple independent verification factors.
Modern best practice now mandates phishing-resistant authentication such as FIDO2 hardware keys or passkeys. SMS and push-based MFA are increasingly vulnerable to sophisticated social engineering attacks.
Passwords alone are insufficient.
Conditional and context-aware access (CA)
CA moves authorization beyond static roles. The access decision is a real-time, dynamic calculation that evaluates a comprehensive set of data points:
- Identity: User's role and privileges.
- Device Posture: Is the device encrypted? Is the anti-virus running? Is it patched?
- Location: Is the access from an expected geography?
- Risk Score: Is the user's current behavior anomalous?
- Resource Sensitivity: Is the resource highly confidential?
Access becomes dynamic and adaptive. A user might be granted access to email but denied access to the billing system until they switch from an untrusted personal laptop to a corporate-managed one.
Privileged Access Management (PAM)
Privileged Access Management (PAM) protects critical, high-risk accounts (administrator, root, service) due to their extensive, "God-like" access across systems.
PAM enforces credential vaulting, session monitoring, just-in-time (JIT) elevation, and the removal of standing administrative privileges.
Reducing excessive privilege is central to modern IAM architecture.
Identity Governance and Administration (IGA)
Identity Governance and Administration (IGA) drives compliance automation and user lifecycle management.
Key IGA functions:
- Automated lifecycle management and compliance.
- Access reviews: Managers confirm the continued necessity of user permissions.
- Role modeling: Standardizing roles organization-wide.
- Segregation-of-duties (SoD): A critical control preventing a single person from having conflicting, high-risk permissions (e.g., creating and approving a purchase order).
Governance transforms IAM from reactive to proactive.
Machine Identity Management (MIM)
In cloud-native, microservices environments, non-human identities often dominate traffic. MIM is the governance of:
- API keys and tokens.
- TLS/SSL certificates.
- Service accounts and secrets.
- Workload identities (used by containers/functions).
Securing these identities is crucial, as their compromise can lead to data exfiltration or massive infrastructure takeovers without any human involvement.
Identity-driven network access: The new security model
The evolution of IAM culminates in identity-driven access.
In a borderless enterprise:
- Network location cannot determine trust
- IP address cannot define legitimacy
- Connectivity cannot imply authorization
Identity becomes the universal control plane.
Identity-driven access enforces:
- Verified user identity
- Validated device posture
- Contextual risk evaluation
- Precise resource authorization
- Continuous verification
Security shifts from:
- Network-centric trust → Identity-centric control
- Implicit trust → Continuous verification
- Static enforcement → Adaptive enforcement
Identity is not merely a component of security. It is the architecture upon which modern enterprise security is built.
Conclusion: Identity as the new perimeter
Cloud permanently redefined enterprise security. The network is no longer the perimeter. Identity is the new perimeter. But identity must be dynamically enforced, not statically assumed. The next phase of this evolution requires enforcing identity at the network layer itself — eliminating implicit trust and restricting connectivity to precisely authorized resources.
That is where Zero Trust Network Access enters the conversation.





.jpg)

