Why VPN fails in cloud environments
In most enterprises, one stolen credential is all it takes to gain network-wide visibility.
Cloud transformation delivered flexibility, and dismantled the perimeter that once protected enterprise networks. SaaS applications, hybrid work, multi-cloud deployments, APIs, and machine identities have created a fragmented security landscape.
VPN was designed for a world where infrastructure was centralized and predictable. In today’s cloud environments, that assumption no longer holds.
Once authenticated, users are logically inside the corporate network.
This creates several risks:
- Broad network visibility
- Lateral movement
- Excessive exposure
- Implicit trust
If credentials are compromised, attackers gain network presence. VPN extends the perimeter. It does not eliminate it. In a distributed, cloud-native enterprise, the debate between ZTNA vs VPN is no longer theoretical. It is operational.
The core cloud IAM challenges
Organizations now face serious cloud IAM challenges:
- Identity sprawl
Privilege creep - Misconfigured cloud policies
- Shadow IT
- Third-party access risk
- Device trust gaps
- Machine identity explosion
Identity sprawl and fragmentation
Every SaaS platform introduces its own identity store and policy engine.
Without central governance:
- Access becomes siloed
- Compliance reporting becomes difficult
- Shadow accounts proliferate
Most organizations cannot answer that question in real time:
“Who has access to this system right now?”
Excessive privilege creep
- Cloud IAM systems are powerful but complex.
- Permissions accumulate over time.
- Overly permissive roles expand the attack surface.
- Over-privileged identities are prime targets for attackers.
- Excessive privilege remains one of the most common root causes of cloud breaches.
Misconfigured cloud policies
- Fine-grained IAM policies are prone to simple but dangerous misconfigurations.
- Cloud breaches frequently stem not from sophisticated exploits, but from policy mistakes.
Third-party and contractor risk
Vendors and partners require system access. Without precise, time-bound controls:
- Access persists unnecessarily
- External compromise becomes internal breach
Machine identity explosion
Non-human identities — API keys, service accounts, workload identities — dominate cloud environments. Their compromise can result in large-scale infrastructure takeover. Machine identity governance is essential.
ZTNA vs VPN: Architectural differences
Zero Trust Network Access replaces network-level trust with identity-based application access.
VPN was built for centralized infrastructure.
ZTNA was built for distributed environments.
The difference matters.
Why ZTNA is better aligned with cloud-native architecture
ZTNA is inherently aligned with cloud-native architecture. Unlike VPN, it does not require inbound firewall openings or exposed concentrators. Applications remain hidden behind outbound-only connections, significantly reducing external attack surface.
ZTNA integrates directly with modern identity providers (IdPs), enforces application-level segmentation, and scales elastically across SaaS and multi-cloud environments. There is no centralized network gateway bottleneck — access is policy-driven, not location-driven.
In cloud environments where infrastructure is dynamic and distributed, this architectural difference is critical.
The role of device trust in Zero Trust
The modern security decision cannot rely on identity alone. Attackers frequently steal credentials, hijack sessions, or compromise devices to bypass authentication. Device trust validates the integrity and security posture of the endpoint making the request.
Device trust metrics validate, in real-time:
- Compliance Status: Is the device managed by the organization?
- Patch Level: Is the operating system and key software up-to-date?
- Encryption: Is the disk fully encrypted (e.g., BitLocker, FileVault)?
- Endpoint Protection: Is anti-malware/EDR running and up-to-date?
- OS Integrity: Has the OS been tampered with (jailbroken/rooted)?
Modern access decisions must evaluate four integrated variables:
- Who is the identity? (Verified via MFA)
- Is the device trusted? (Verified via EDR/MDM posture)
- What is the risk level? (Verified via behavioral analysis)
- What resource is requested? (Verified via Authorization Policy)
Trust is not a static state; it is continuous. If the conditions change mid-session (e.g., the device's anti-malware turns off, or the user's location jumps across continents), access must be automatically downgraded, limited, or revoked.
How ZTNA eliminates lateral movement
Identity-driven access enables a superior form of network isolation known as microsegmentation, without the complexity of VLAN sprawl and static firewall rules.
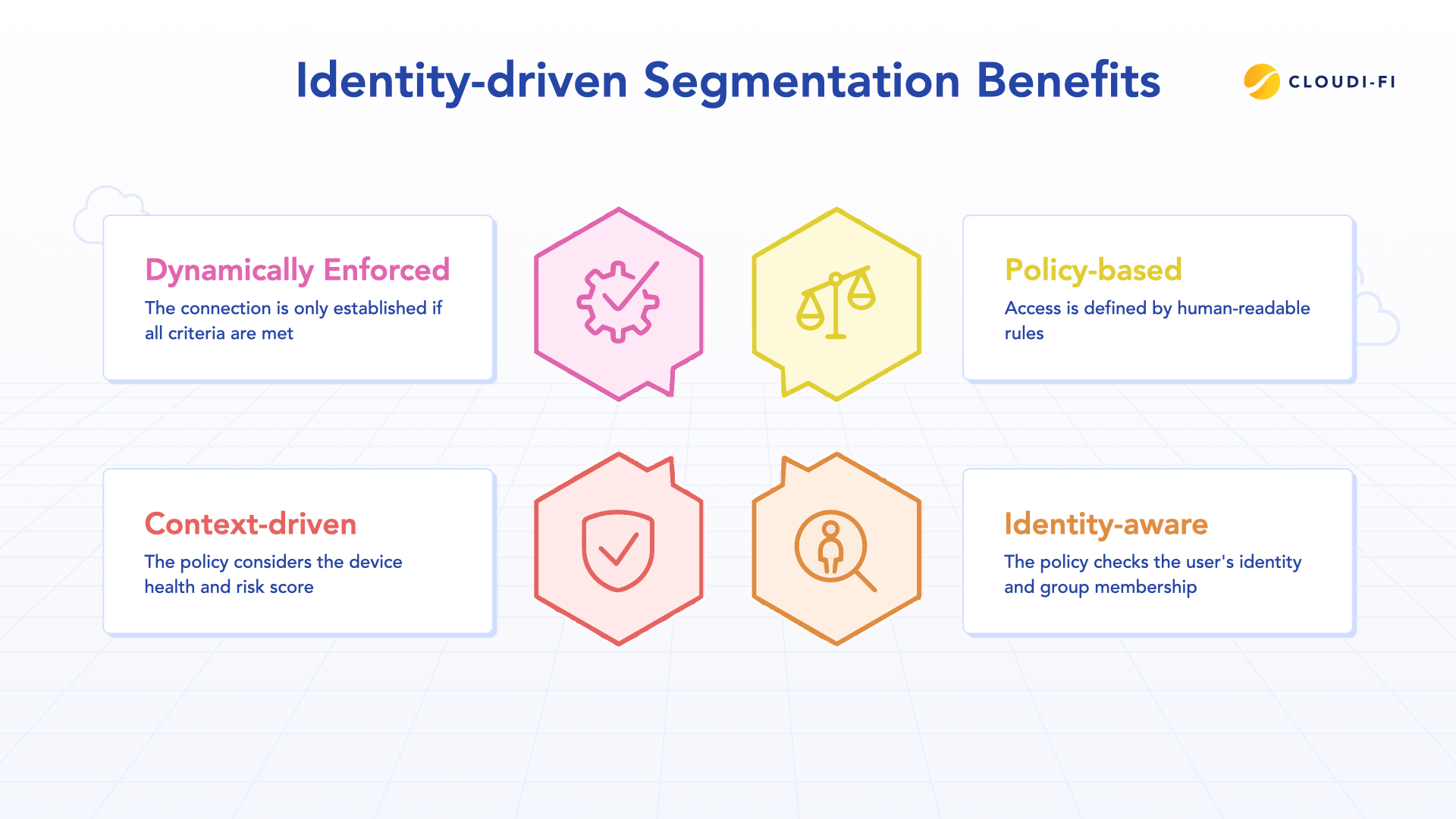
In this model, access is:
- Policy-based: Defined by human-readable rules (e.g., “All Finance Analysts can access the Payroll app.”)
- Identity-aware: The policy checks the user’s identity and group membership
- Context-driven: The policy considers device health and risk score
- Dynamically enforced: The connection is established only if all criteria are met
Unlike VPN, ZTNA does not grant network presence.
The physical network is reduced to a simple, controlled conduit — it is never a trusted zone.
This ZTNA architecture supports:
- Secure, least-privilege remote access for all employees
- Secure third-party collaboration by granting access only to specific files or applications
- Secure BYOD flexibility with appropriate limitations
- Time-limited, just-in-time privileged access for maintenance tasks
By removing implicit trust and restricting access to specific applications rather than networks, ZTNA eliminates the conditions required for lateral movement.
Replacing VPN with ZTNA: A practical migration path
Replacing VPN with ZTNA reduces:
- Attack surface
- Lateral movement risk
- Overexposed infrastructure
It enables granular access control, continuous verification, policy visibility, and alignment with cloud-native architectures.
To effectively transition:
- Audit existing network exposure and VPN access policies
- Identify high-risk and high-value applications
- Deploy ZTNA alongside VPN in a phased rollout
- Migrate remote and third-party users first
- Enforce least-privilege application access
- Decommission broad network-level access
- Integrate telemetry into SecOps workflows
ZTNA operationalizes Zero Trust principles while enabling secure, scalable cloud operations.
Best practices for identity-driven access
To comprehensively address cloud IAM challenges:
- Treat identity as core infrastructure
- Eliminate implicit trust
- Enforce phishing-resistant MFA
- Implement least privilege
- Integrate device posture signals
- Automate lifecycle management
- Secure machine identities
- Integrate IAM telemetry with SecOps
Identity-driven access must be enforced everywhere — across SaaS, cloud workloads, APIs, and endpoints.
Conclusion: Connectivity must be identity-governed
The cloud dissolved the perimeter. VPN attempts to stretch it. ZTNA removes it entirely. In a borderless enterprise, connectivity must be governed by identity, device trust, and continuous verification. ZTNA vs VPN is not just a technology comparison. It is the difference between extending outdated trust and enforcing modern Zero Trust Network Access. Organizations that solve their cloud IAM challenges by replacing VPN with identity-driven access will dramatically reduce risk while enabling secure, scalable cloud operations.
FAQ: ZTNA vs VPN
Is ZTNA more secure than VPN?
ZTNA reduces risk by eliminating network-level access and enforcing continuous identity and device verification. VPN grants broad network access after authentication, increasing exposure.
Can ZTNA completely replace VPN?
In most modern cloud and hybrid environments, yes. ZTNA provides application-level access without exposing the corporate network.
Does ZTNA prevent lateral movement?
Yes. Because users never gain network presence, unauthorized systems remain invisible and unreachable.
What role does device trust play in Zero Trust?
Device trust ensures that access decisions consider endpoint security posture, not just user identity, reducing the risk of compromised devices gaining access.
Is ZTNA suitable for third-party access?
Yes. ZTNA enables precise, application-specific, time-bound access for vendors and contractors without exposing internal networks.





.jpg)

